CYBER SECURITY, ITS IMPORTANCE IN BANKING AND PRECAUTIONS
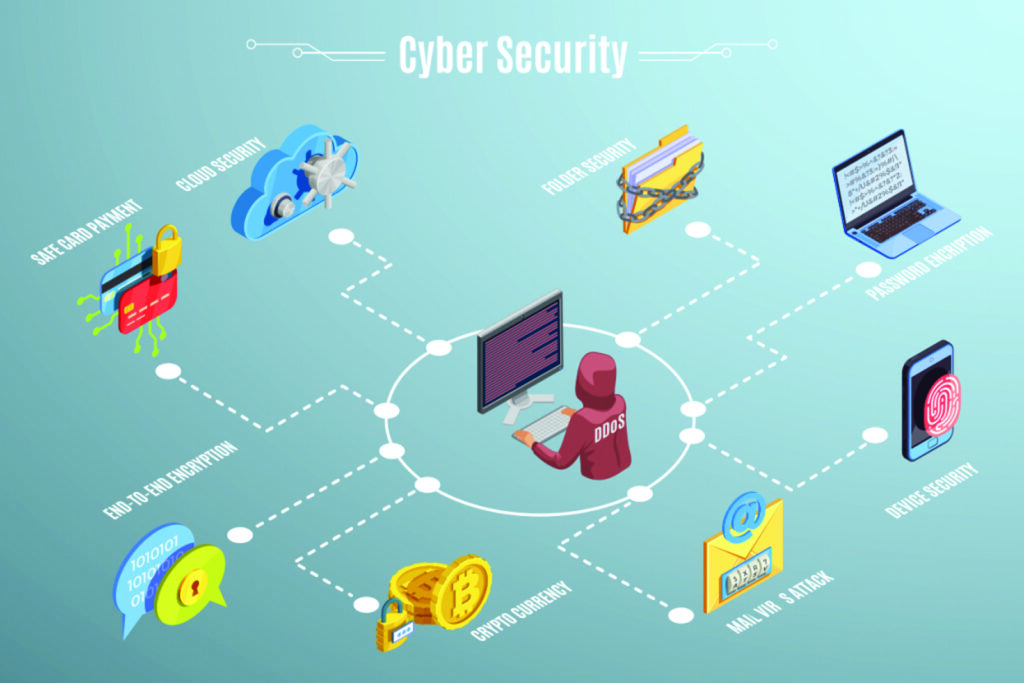
Cyber Security has become a major requirement forall the individuals and organisations that are doing any of the activity related to IT (information technology), as there is a major threat from various sources involved in cyber crime. Cyber Security provides the protection from any damage to software, hardware, network or electronic data from such external sources.
The extensive usage of internet and digitisation in most of the organisations including banks has also increased the Cyber risks to the people engaged or linked to these organisations especially to those using digital platform. That’s why most of the organisationsare having their own Cyber Security Policies so that it can be a guiding light for the employees working in those organisations because if those measures are not adhered, it may result in loss of data as well as financial loss to customers as well as to the bank which may lead to loss of reputation to such organisations and their integrity may also become doubtful.
In earlier times, most of us were doing transactions through banking sector by going physically. But with the increase of digitisation and time constraints organisations being technology driven, customers especially those of new generation are doing their transactions on one or another digital platform as per their ease of use and availability. Earlier for doing digital transactions, a person used to go to cyber café. But later on, those who were able to afford were doing the same on their laptops. But now most of the transactions are being done onmobile. But due to lack of awareness or carelessness, very less persons are taking security in their mobiles. They are not using antivirus for their mobiles so that they can save their mobile and hence the data and personal information stored in it from unauthorized access as well as from downloading of any harmful content.
Cyber Security threats include many types of Social Engineering threats. The mostly used threats are described below in brief:
Phishing: It is most common among users who are not well versed in browsing the internet and online resources. It is used to obtain sensitive/confidential information such as login credentials, account details etc. Very often, phishing is done by e-mail.
Spear Phishing: It is similar to phishing, the difference being that spear phishing emails are carefully designed to a specific individual, organisation or a group. Such mails are having a link to some malicious website to get someone unknowingly and unintentionally downloading a piece of malware to release some sensitive information.
Spoofing: The word ‘spoof’ means to hoax, trick or deceive. Therefore, in the IT world , spoofing refers tricking or deceiving computer systems or other computer users. It is a type of attack to gain unauthorized access to computers . This is typically done by hiding one’s identity or faking the identity of another user on the internet. E-mail spoofing involves sending messages from abogus e mail address of another user.
Identity Spoofing : A method of deception by using another IP address (that is not your own) to access the network that is usually used as on-line camouflage to mask their activities and/or gain unauthorized entry. In other words, it refers to the action of assuming the identity of some other entity and using that identity to accomplish a goal.

Vishing : Vishing is short name of voice phishing which is used to solicit private, personal or financial information through phone calls.
Smishing: Also known as SMS phishing, this method uses text messages in order to deceive recipients to solicit personal information.
Pharming: It is the fraudulent practice of directing Internet users to a bogus/fraudulent website which appears to be a legitimate one, in order to obtain personal information .
Baiting: It is somewhat similar to a phishing attack . It relies on the greed or curiosity of a victim. However, what distinguishes them from other types of social engineering is the promise of an item or good that hackers use to entice victims.
Pretexting: – A Pretext is a false motive. Pretexting is a form of social engineering where attackers lie to obtain privileged data. They focus on creating a good pretext, or a fabricated scenario, that they can use to try and steal their victims’ personal information. Such persons pretend to need information in order to confirm the identity of the person they are talking to. After establishing trust with the targeted individual, the pretexter might ask a series of questions designed to gather key individual identifiers such as confirmation of the individual’s social security number, mother’s maiden name, place or date of birth or account number.
Importance of Cyber Security in Banking
In case of Banking Sector, the importance of cyber security is to protect the customer details whether it is personal or account related information. This is a tech savvy era and more and more persons are going for a less cash transactions; activities and payments are being done through online transactions. There have been many cases in the past where the systems of the banks were hacked and they had to bear financial losses due to which the trust of their customers is lost and hence the customer base.
The major cyber threats which the customers are facing are through more and more use of mobile applications in which they are doing transactions with having a link to their account details. The customers are giving access to all the details even if they are not required for every application. Besides, the customers are not using any security measures for saving their data.
Precautions to be taken for Cyber Security:
We have discussed various types of Cyber Security threats. Now it is necessary to discuss about the basic precautions that can be taken for preventing such type of threats. Some of them are discussed below:
Desktop Security: It is very much necessary to keep our desktop secure. It starts from locking the desktop whenever we are leaving our seat. The locking of the screen can be done by pressing Alt+Ctrl+Deland then selecting the option of locking the computer. But the same can also be done in fraction of a second by simply using the combination of Windows+L .It preventsthe data of our desktop being misused or deleted by any of our colleague/customer having any malafide intention and who may use this opportunity of misusing our system if it is found unlocked/open at some point of time. Besides, some more precautions are necessary to be taken for securing our data in our PC. It includes keeping our desktop screen clear and minimum files should be present on it as desktop is a part of C:\ drive and if due to any reason, the hard disk is formatted, all the files present in C:\ drive are difficult to recover. So, it is advised to keep our important files in any drive other than C:\ . We may have some files which may be of daily use. In such case, we can create a shortcut of the same on the desktop and use it. Also, sharing of folders should be avoided because when we share a folder, all the contents available in the folder become available to all the network users and are prone to risk. So, if it is very necessary to share some content or file on the network , share that particular file instead of full folder.
Password Security:Password security is very much important for every application, whether it is desktop or any mobile application. Often, it is seen that in offices, either the passwords kept by the users for their systems are same or known to their colleagues. It is very risky, as the data available in the system as well as their personal information/files are available to all. The password for any of the application should not be simple so as to be guessed by anybody and it should not include name, date of birth, anniversary, any other personal information or having ‘easy to guess’ clues. The password used should be long and a strong one which is difficult to guess and should be a combination of numbers, upper, lower & special characters. A zero can be used for substituting the letter O or @ can be used for the letter A. The longer and more complex the password is, harder it is to crack. It can be a nonsense phrase or grammatically incorrect phrase. But sequentially words/numbers on a keyboard such as qwerty9876 should be avoided. If a phrase is used as a password, better to capitalize the first letter of each new word, which will be easier to remember. The password should be changed often and especially if we have a doubt that somebody has come to know about our password. Although, it is very difficult to keep different passwords for various applications, but still it is advisable to do the same. Also, reuse of passwords should be avoided. It is also very important to keep our passwords safe and secure and at a place in our mobile/computer which is not within plain sight of other people (never on sticky notes on our work computer). Even if we are storing a list of passwords or password hint sheet in a document file in computer/mobile, name it randomly so that it is not easy to guess by snoopers and better to have a master password for that file (which at least should not be forgotten.). Besides, it is also to ensure that password should not be shared over the phone. Even if there is an urgency for the same, it should be shared in the form of a code or by splitting it and sending it.
Anti-Virus Security: Our Computers/Mobiles are most vulnerable to threats from virus attacks and being attacked by malware which can be avoided by taking proper measures and installing authentic antivirus softwares. Most of the organizations are using one or another antivirus softwares in their systems and mostly all the systems are monitored centrally by the particular team taking care of it. These softwares are updated regularly and periodically by these teams and such systems which are not taking part or are switched off at the time of such updation are then kept out of network till being updated so that the threat and spread of malware/virus can be avoided. Besides the official computers, it is very necessary to use the anti-virus on our laptops, PCs as well as on our mobiles. In earlier times, internet banking was mostly done on our Laptops or on our PCs. But now- a- days, the maximum percentage of online transactions whether it is through internet banking or through any of the various mobile applications/UPI/BHIM etc., is done through our mobiles, but still a very less percentage of users are using anti-virus software on their mobiles either due to non-awareness or due to ignorance, although these anti-virus softwares are not too costly and are also available on e-commerce sites. But it is not advisable to use anti-virus softwares which are free of cost as these may be even more dangerous than not using any of the paid ones, because these free ones may steal the data and they also run many applications in the background which may even hang the mobile and hamper its working.
Internet Security:It is very much necessary to be careful regarding internet security. All the applications which are requiring internet are prone to risk. So, it is essential that we have to be very careful while logging into internet sites. Internet security is related not only to internet, but also to browser security, network security and the World Wide Web. Whenever we are logging into any internet site for doing any transaction, we have to ensure that the network is secured with https. HTTPS is an internet communication protocol that protects the integrity and confidentiality of data between the user’s computer and the site. Users expect a secure and private online experience when using such website. HTTPS uses an encryption protocol to encrypt communications. The secure site can also be recognized with a padlock in the address bar. The “S” in HTTPS stands for “Secure”. It’s the secure version of the standard “hypertext transfer protocol”. So, while browsing any site for doing any transaction, it is to be ensured that we are using a secure site and not on a compromised network that is redirecting to an impostor website. Although, now cyber cafe are used very less for doing online financial transactions, still if a person is going to cyber café for the same, it is advised to use virtual key board (if available with the application) for using any login details and password, because key loggers might have been used in the keyboards to steal the data you feed through the keyboards while the sequence of virtual key boards change every time.Besides, at many places such as hotels , railway stations , airport etc. , free Wi-Fi is available which is often used by the persons using internet in that particular area. But, as free Wi-Fi is available to all those having access to it, it is also more prone to risk. Hence, it is better to avoid using any such Wi-Fi which is not secured especially for doing financial transactions. Both password-protected and unprotected public Wi-Fi connections can be easily monitored by third parties by employing very simple measures, for example by imitating networks. It is better to use mobile hotspot from our own smart phone. Hence, it is to be remembered that Wi-Fi connection is extremely unsafe until the standard safety precautions are not followed.
E-mail Security: E mail is the most effective means of communication in our constantly evolving world of technology. It has become more versatile than any other form of communication and is popular for personal information as well as for corporate communication. We rely heavily on e-mail as a trusted channel for communication , but there is an increasing threat of sensitive data loss in today’s world due to vulnerability to malicious e-mail attacks.It is very much important to take proper security measures in e-mail for protecting our personal information as for hackers/crackers, e mail is the easiest way to gain access to sensitive personal information. They use the method of phishing, spear phishing, malware delivery etc. for the same. A way to detect malicious e-mails is through filters. Filters are designed to examine specific patterns and content items in an e-mail to recognize a message as spam or malware,including URLs, attachments, headers or message text. So, it is to be ensured that spam filters should be kept updated for effective e-mail security. Now-a-days , e-mails are exchanged for the purpose of transactions on e-commerce sites, education, trading etc. Now phishing, spear phishing or spoofing e-mails are the biggest threat for an individual or an organization because these mails may contain some malware or link which may be clicked by a person and personal informationmay be given which may be misused for gaining unauthorized access to the bank account .Although .zip files may be the most common ones to carry malware and .pdf files are safest to open, but, in principle, all files may contain malware . This includes .pdf, .jpg, .png, .rar, .exe, etc. Therefore, be extremely cautious with opening any attachment that is suspicious. Hence, it is very necessary that e-mails from unknown sources must not be opened or forwarded and should be deleted and we should be very skeptical of offers or messages where we need to install or open something . Besides, e-mails in the mail box should be kept to a bare minimum, because storage, whether it is Google Drive or official one has a limited storage space and the mails will not be received after its capacity is full and the coming mails will bounce bank and hence we may miss some of our important e-mails due to this reason.
Debit/ Credit Card Security: In this tech savvy era, details of debit or credit card are used in most of the e-commerce transactions . So , it is very necessary to be very careful while using the details of debit/credit card in any of e-commerce sites/POS or while using our debit card in any of the ATM. While using debit card in ATM , it is to be ensured by the users to check that any skimmers are not used in the ATM, through which details of the card can be copied and misused. Similarly for the bankers, care should be taken that the ATMs are checked for skimmers now and then and CCTVs should always be in working mode so that if CCTV footage is required at any point of time for some disputed transaction, it is readily available. Besides, the user should not give OTP /CVV/PIN to any unknown person. A majority of the transactions are now-a-days done through UPI and the fraudulent persons are often asking OTP and the users often give the OTP when asked for the same for receiving money by the fraudsters due to being unaware of the fact that OTP is not required in case of receiving money but only at the time when account is to be debited for any payment. Also, the CVV written on the back side of the card should be memorised after receiving the card and then a small opaque sticker should be pasted on it or it should be simply erased from the card.
The last , but not the least, if we feel that there is some phishing activity or some malware or virus has attacked our system, it should be informed to the IT team of the organization we are working in through phone or e-mail and there assistance should be taken.




